Foldr provides two different options for two factor authentication. Firstly, there is a built-in 2FA mechanism in the Foldr appliance, or following server update Update 4.10.3.2(3rd October 2018) introduces support for integration with the popular third party 2FA service from Duo.
The administrator must select one type of 2FA for use globally. It is not possible to use Duo for selected users/groups and the built-in feature for other users.
Differences between Foldr 2FA v Duo 2FA
Foldr 2FA uses One Time Password (OTP) codes exclusively utilising the TOTP open standard. The generated passcode is temporary and valid certain amount of time. Users must install an app (or browser extension), which calculates the OTP code based on a secret “seed” and current time. TOTP is an implemented by multiple apps including Google Authenticator and the Authy app. These popular apps are available for iOS and Android.
Both 2FA options allow users to optionally trust certain devices so they do not have to supply the 2FA codes with each sign-in attempt. The administrator can also specify a network to be considered trusted (usually inside the corporate LAN) where users will not be required to provide 2FA codes.
Duo users must install the third party Duo Mobile app in order to authenticate successfully. Duo can provide standard OTP codes through the mobile app, but also offers the convenience of OneTouch push notifications where a user can simply agree to a Yes | No prompt on their smartphone / tablet to authorise the sign-in attempt. Finally Duo offers a voice call service, where the user receive the passcode from an automated call service to their designated phone number.
Enabling Duo 2FA Support
It is vital that the Foldr appliance’s system clock is accurate – You can check the appliance time from within Foldr Settings (show top right of the UI) or by running the date command from the console when signed in as fadmin. Should you need to correct the appliance time, this can either be done by correcting the host clock (VMware ESXi etc) or if using NTP in Foldr Settings >> General >> Time Settings and obtain time from a local domain controller.
You can force the appliance’s clock to be synchronised with an NTP time source using the console command:
time-sync IP-address-of-domain-controller
Foldr must be added to the Duo admin console as a protected application. To do this sign in using administrative credentials at https://duo.com.
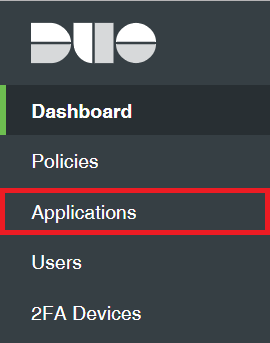
Click Applications
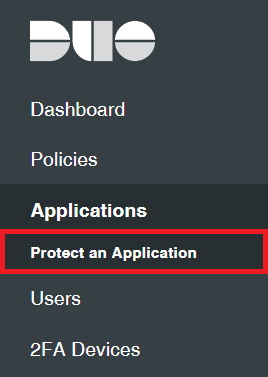
Click Protect an Application
Search for ‘Web SDK’ and select it from the apps list by selecting Protect this Application

The app detail summary will be displayed showing the Integration key, secret and API hostname.
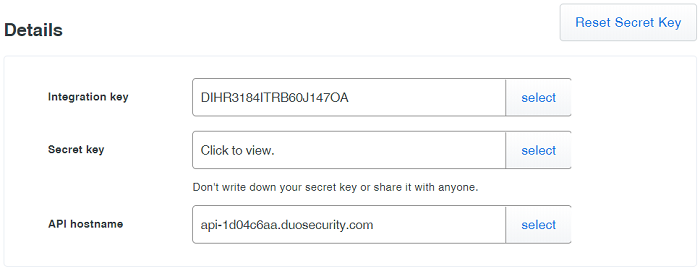
Click Select to reveal / highlight each of these values in turn copy/paste and populate the corresponding fields within Foldr Settings >> Two Factor >> Settings. Note that the 2FA Provider must be first changed to ‘Duo’ from ‘Foldr’ which is default.
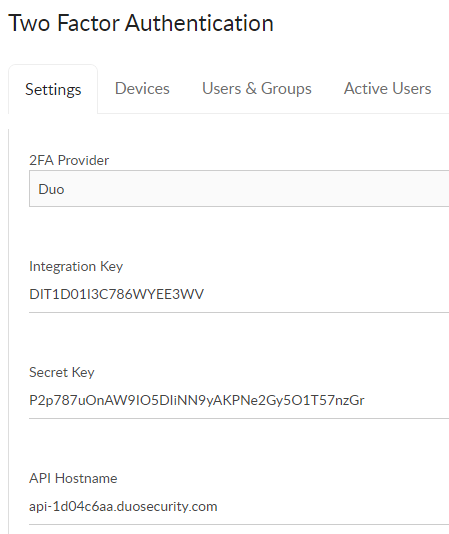
Scroll down and click the highlighted text to generate a random application key
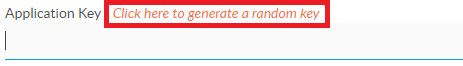
The application key will be now displayed. With the Duo fields populated, now click Save (top right)
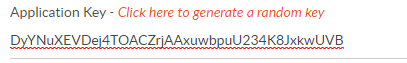
Navigate back to the Duo admin console and scroll down to the Settings section and provide a suitable name for the integration.
Scroll down to the bottom of the page and click Save
Navigate back to the Foldr Settings >> Two Factor >> Settings page and optionally allow users to trust their Duo device. This will allow them to only pass Duo 2FA on the device once. Leave this setting to ‘Off’ if you wish users to pass Duo 2FA for all login attempts.

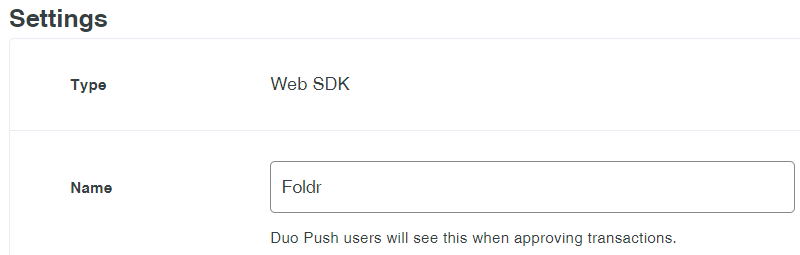
Optionally, configure a trusted network (location) by IP address or subnet where 2FA is not required. This is typically used so users are not required to provide 2FA codes when inside the corporate network.
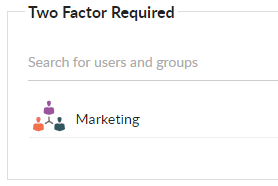
Navigate to Foldr Settings >> Two Factor >> Users & Groups. This screen provides mandatory or optional 2FA policies for individual users or groups. To enforce Duo 2FA for all users in the Marketing group for example, configure as below.
If Two Factor Optional is used, a user can enable 2FA on their account at a time of their choosing via the Foldr web app >> Me tab.
User enrollment in Duo 2FA
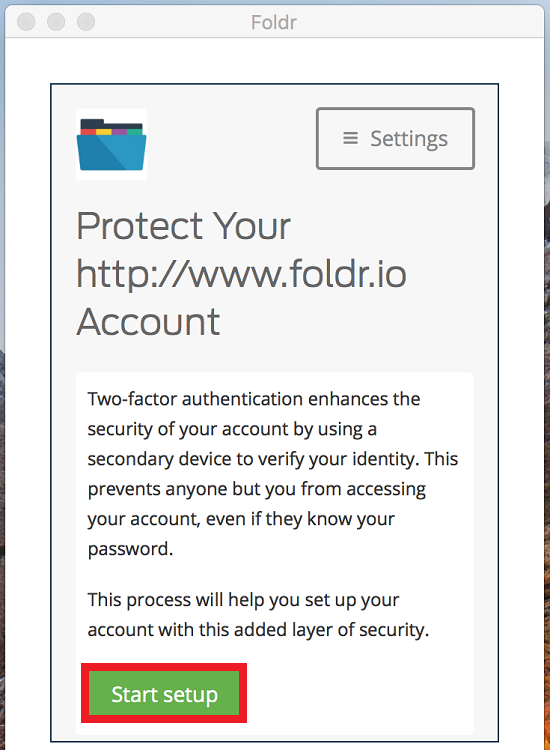
When a user next signs into Foldr via the web, Windows or macOS apps and they are required to use Duo 2FA they will be shown the enrollment screen after providing their Active Directory credentials.
Note that iOS and Android apps will receive updates during 2019 to support Duo 2FA sign-in (apps require web sign-in for Duo support or other 2FA / SSO solutions).
Click Start setup
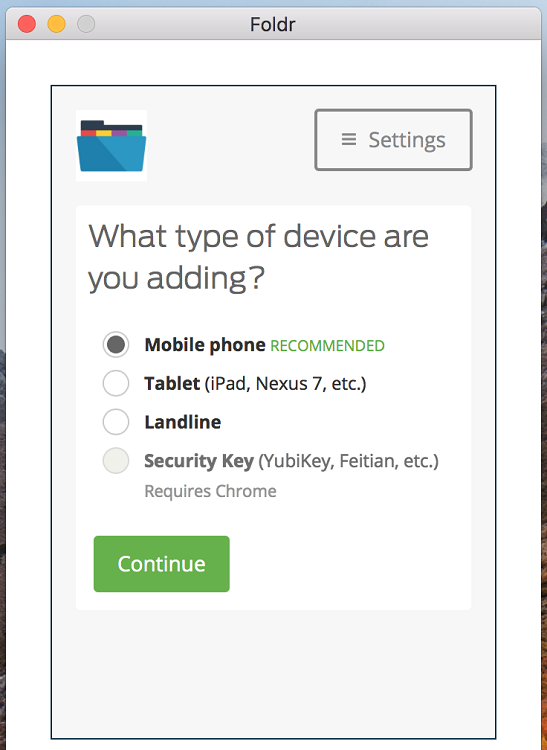
Select the type of device and click Continue. Mobile phone is recommended and is used in this example
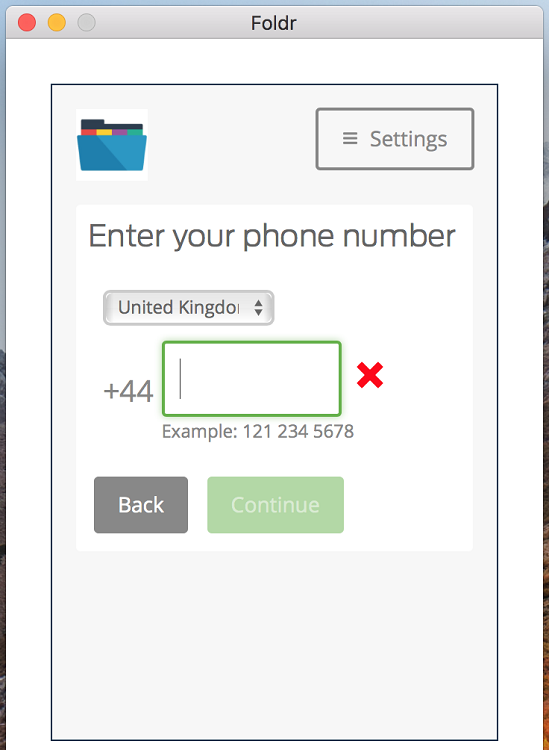
Enter your phone number and country code and click Continue. Note a pop up checkbox will appear that you must check before you can click Continue
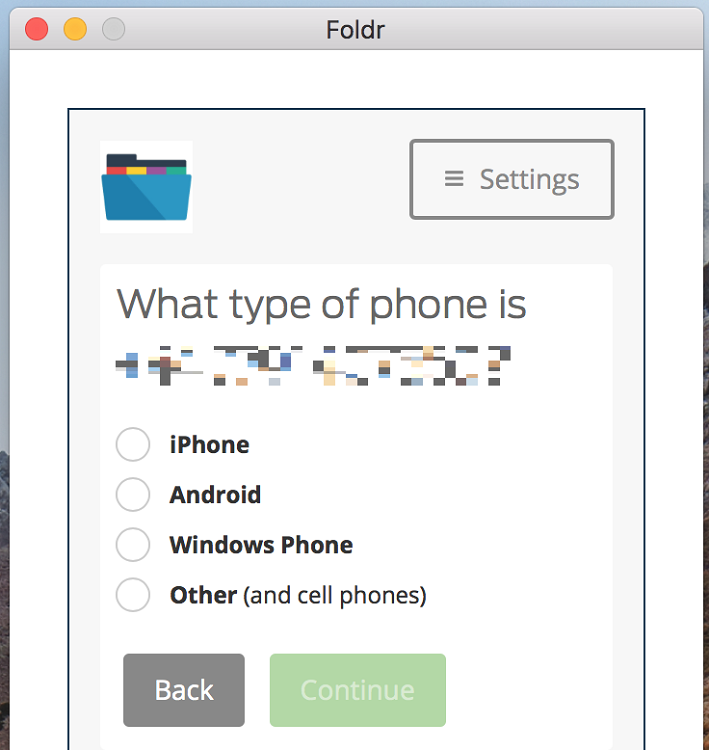
Confirm the phone type from the given options and click Continue. In this example we will use iPhone.
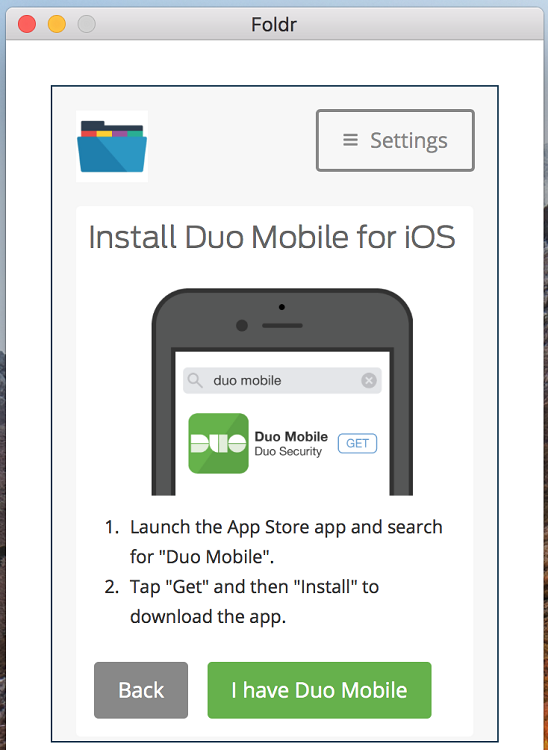
Install the Duo Mobile app from the App Store or Google Play if not already installed. Once installed, click I have Duo Mobile
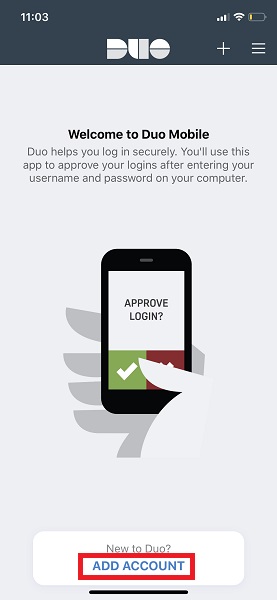
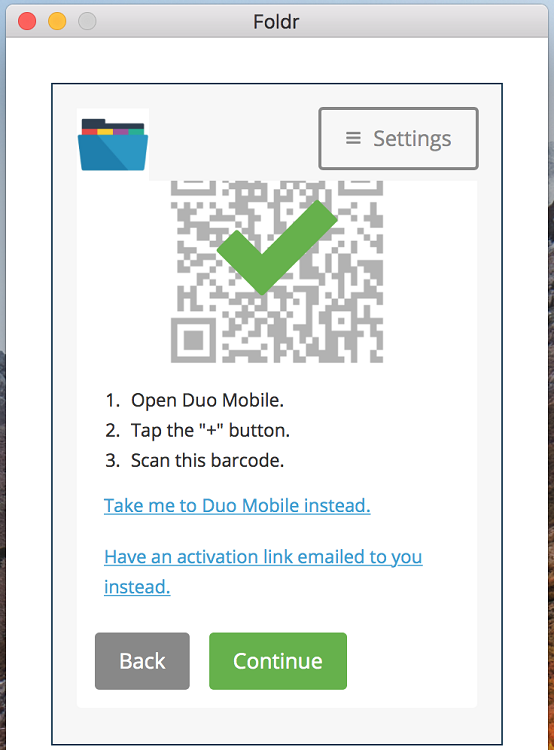
A QR code will be presented on-screen. At this point the user should open the Duo app on their smartphone and tap Add Account or use the + button top right.
You will have to allow Duo to use the device camera and once the QR code has been scanned, the graphic on-screen in the setup dialog will update. Scroll down and click Continue
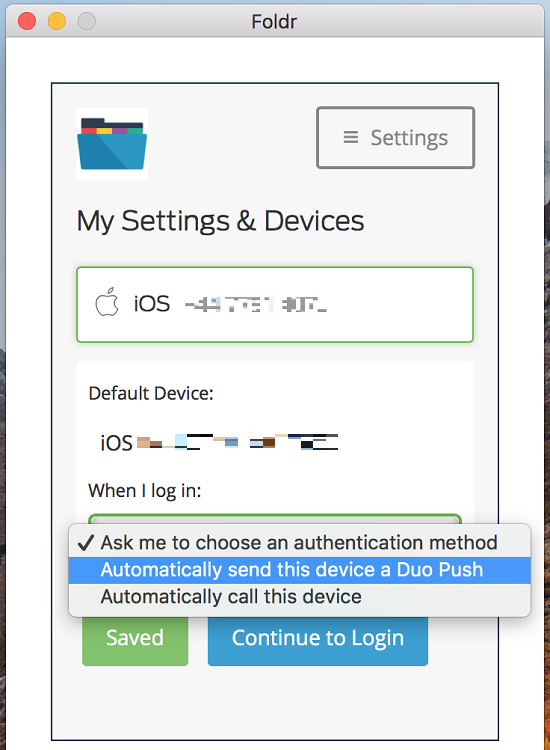
Click Continue to Login or choose from the preferences on how Duo should behave when signing into Foldr.
A push notification will be sent to the users device and they can confirm it within the Duo Mobile app
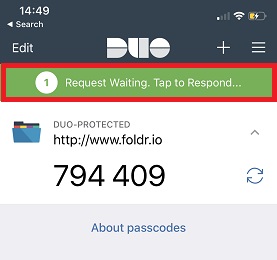
Tap the area highlighted in the Duo Mobile app to Allow / Deny the sign in request
Tap Approve
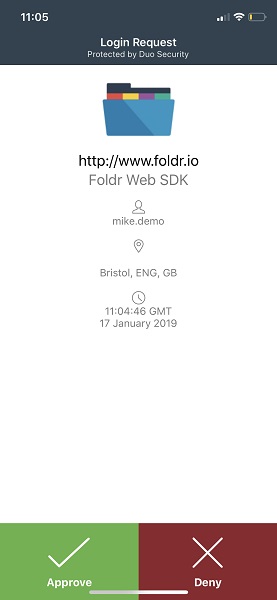
The user will now sign into Foldr and setup of their device / app is complete. All subsuquent sign-in attempts to Foldr will prompt them with the following dialog. Note if users were allowed to trusted devices and they selected to trust the device during enrollment, the user will sign in without being challenged during future sign-in attempts to Foldr on that particular device.
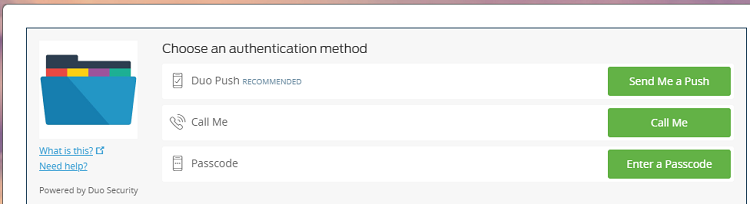
Click Send Me a Push and Approve the request in the Duo app to complete sign.