Foldr v4 allows you to run multiple independent instances of Foldr for any number of subdomains. Each subdomain / customer tenant instance is licenced and configured separately and provides the ability to support environments that run numerous Active Directory domains from a single virtual appliance or cluster of appliances.
Typical usage scenarios for multi-tenant mode would be a service provider providing hosted file access services to multiple customers. Each tenant organisation (customer) would access Foldr using their dedicated tenant subdomain. i.e.
https://apples.yourdomain.com
https://oranges.yourdomain.com
Multi-tenant mode can only be managed from the virtual appliance console using the following commands.
Enable multi-tenant mode
To enable multi-tenant mode:
tenant-enable
![]()
Create a new tenant
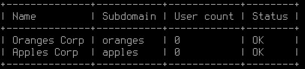
To create a tenant:
tenant-add “name-of-customer” subdomain
For example, to create a tenant called Apples Corp that will use the subdomain apples. The use of quote marks as shown is important when creating a multi-worded tenant name:
![]()
The tenant and the default built-in security groups will be created automatically:
List all tenants
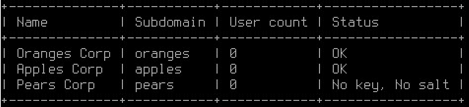
To list all tenants and show the user count for each instance:
tenant-list
Remove a tenant
To remove a tenant:
tenant-remove subdomain
Please note that this does not remove any user files. Just the tenant subdomain and it’s configuration.
Tenants in an Infrastructure and Client Access Deployment
If you have deployed Foldr with infrastructure and client access appliances, each appliance in the deployment should firstly be placed into multi-tenancy mode by running ‘tenant-enable’. Once this has been done you can create your tenants as required on one of the appliances.
Syncing Tenants (IMPORTANT)
After creating your tenants you must synchronise the tenant’s encryption keys across all other Foldr appliances before the tenant subdomains are usable. The following command should be run from the Foldr appliance upon which all the tenants were created on.
The STATUS column when running tenant-list should state ‘OK’, if the appliance is missing the keys you must run tenant-sync from another appliance that can provide them. If you attempt to run tenant-sync from an appliance with missing keys, an error will be displayed and the sync operation will be aborted.
In the example below, Pears Corp (https://pears.yourdomain.internal) is currently unusable on this system due to missing encryption keys:
Tenant-sync command example :
tenant-sync appliance-ip-1 appliance-ip-2 appliance-ip-3 -p password
The -p argument used above is optional and will only work if all appliances are using the same fadmin password. Otherwise you will be asked to provide a password for each appliance individually.
This command ensures that all appliances use the same encryption and hashing keys for individual tenants. For correct operation these keys must be synced between all client access appliances. It is also recommended that you sync them with your infrastructure appliances as well but this is not vital.
Disable multi-tenant mode
To disable multi-tenant mode:
tenant-disable
DNS & multi-tenant mode
DNS must be correctly configured, both internally and externally for multi-tenant mode to work correctly. If one does not already exist, a lookup zone should be created for the domain name and Host / A records created for each tenant. Each A record must be configured to resolve to the IP address of the Foldr appliance.
It is also vital that the preferred and secondary DNS servers that are configured on the Foldr appliance can resolve all customer Active Directory domains that are used. Also all paths (LDAP servers, shares, home folders and so on) must configured fully qualified.
Configuring & Licensing Tenants
The administrative fadmin account can configure each tenant by browsing to:
https://tenant-subdomain.yourdomain.com/settings
The tenant instance can then be configured as normal.
NOTE – The default /settings page at https://IP-address-of-Foldr/settings serves no purpose in multi-tenant mode and should not be used.
Delegating Administration of the Tenant
When each new tenant is created, the administrator can sign into the tenant’s settings admin UI (https://tenant-subdomain.yourdomain.com/settings) as fadmin and delegate administrative permissions to either local or Active Directory users.
See here for more information.