Controlling who can access Foldr
Within Foldr Settings >> Security, the Foldr administrator can control which users/groups are permitted to use any of the Foldr apps (applies to web, mobile and desktop) with the Use Foldr permission. There is an additional permission for ‘Connect via WebDAV‘ on the same screen to control access via WebDAV clients.
‘Use Foldr’ will by default contain the built-in ‘Foldr Users’ group with an ‘Allow’ permission for both Foldr and WebDAV.
The built-in Foldr Users group = Everyone and as such will allow any user with valid credentials to sign in.
To restrict access to Foldr and only permit one or more specific Active Directory groups, remove the ‘Foldr Users’ item and Click ‘Add User or Group’ to search for the LDAP users or groups that you wish to apply permissions. Note that Foldr will only search the domain within the scope the LDAP Search DN configured in the General section.
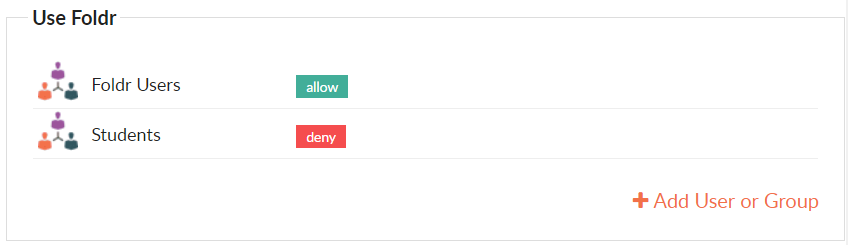
‘Deny’ entries always override ‘Allow’, the exception being where individual user permissions override groups.
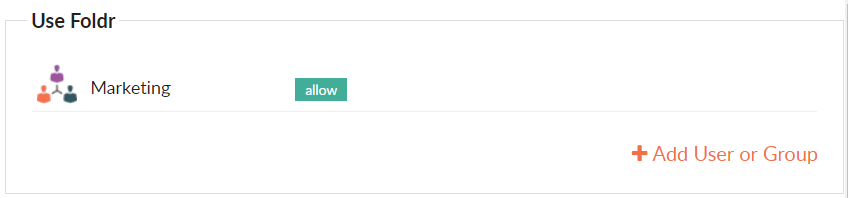
Example 1 – Only allow Marketing group users:
Example 2 – Allow all users but deny Students:
The administrator can create granular access rules for users / groups by location (IP address or subnet) when configuring these permissions. i.e. Allow specific users or groups to only use Foldr on-premise or from a specific location. More information on location based access policies can be found here
Storing passwords
To provide support for existing and future product functionality (such as integration with other services), Foldr v4 automatically stores user’s passwords once they have authenticated. Passwords are stored within an internal database and all values are encrypted using OpenSSL and the AES-256-CBC cipher. Furthermore, all encrypted values are signed with a message authentication code (MAC) to detect any modifications to the encrypted string.
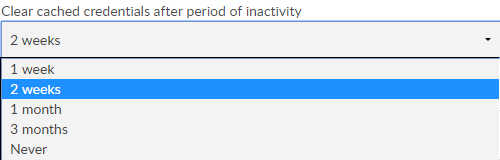
By default the Foldr appliance will delete a users cached password after 2 weeks of inactivity. This is configurable within Foldr Settings >> Security >> Passwords >> Cleared cached credentials after a period of inactivity.
In Foldr v4 administrators can optionally deploy Foldr so that the database containing configuration and other data (such as user credentials) is stored on a central, non-internet facing system and all user interaction takes place via satellite client access appliances.
The administrator has the option to disable storing users passwords completely. This configuration would require the use of a service account to be configured on all SMB shares and enable the setting ‘use service account for all access’ on the share. The appliance would then connect using the service account on behalf of a user making the request. There is an additional setting labelled ‘Enable full ACL support’ to parse a users individual NTFS permissions so they receive the appropriate level of access to the shares.
Password Change Control (Active Directory Only)
Foldr v4 now provides users with Active Directory password control and password expiration handling for users connecting via a web browser or the native iOS / Android apps.
IMPORTANT – Password change control requires the Active Directory domain to be using LDAPS. If LDAPS is not being used you will see the following message:

Users are able change the network password at a time of their choosing from the web, mobile or desktop apps. Another benefit to enabling password reset in Foldr is when the organisation has a password expiration policy. With this feature enabled, and a user attempts to log into Foldr using an expired password they will be prompted to change it.
Similarly, if the ‘user must change password at next login’ flag is enabled in Active Directory for a user, Foldr will also allow the user to change their password as they log in. This applies to the web, desktop and mobile apps.
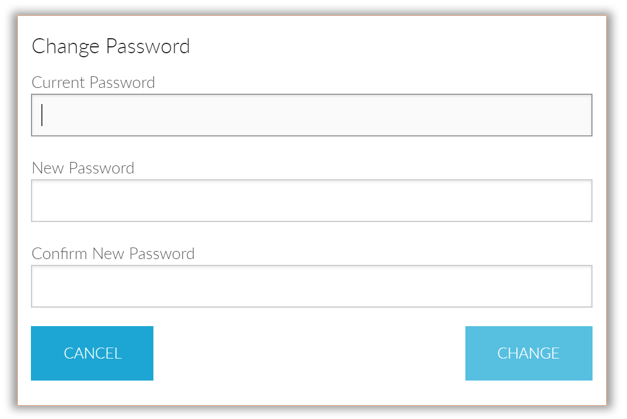
By default, password control (and all other password features) is disabled, however, the administrator can enable this feature within the Security >> Passwords tab.
Authentication Rate Limiting
Foldr v4 includes a default limit set that will prevent a user signing in after 10 failed attempts in one minute. The user will then need to wait a further 60 seconds before any login attempts will be processed. This feature has been designed to mitigate against malicious attacks on the service such as brute force attempts on account passwords.
Trusted Proxies (Reverse Proxy Support) & X-Forwarded-For
If your network environment uses a reverse proxy or some other web publishing service to present Foldr externally, the IP address of the LAN facing network interface of the firewall or other device performing this role should be entered within Appliance >> Network >> Trusted Proxies.
A reverse proxy removes the need for a dedicated public IP address when accessing Foldr externally. This brings obvious benefits however you may notice that the client IP address shown in the Foldr audit logs is incorrect. This is due to the fact that the source IP address of all network packets that reach the Foldr appliance(s) are showing the address of reverse proxy/firewall rather than the client’s actual IP address.
To resolve this, you should configure your reverse proxy/firewall to enable the X-Forwarded-For HTTP header for all traffic destined for your Foldr appliance(s). Once this has been done and the IP address of the reverse proxy/firewall / load balancer has been configured within Trusted Proxies, the Foldr Activity log will display the client’s actual IP address.
More information on X-Forwarded-For header can be found here.
Other Security Considerations – Mobile Devices
Mobile devices (iOS & Android) running the native Foldr app provide the ability to enforce passcodes, PIN or TouchID to protect access to corporate resources. Foldr also provides the ability to store credentials to allow convenient login from these devices (using best practices such as the iOS keychain and Android private shared preferences).
However, in the event of a mobile device becoming lost or stolen it should be considered important to remove the ability to sign in from the lost device, or continue a user session if the device is running a session of the Foldr app and it is already signed in.
Using Foldr v4, a user can quickly revoke access to the device by logging into the web app’s, Me >> My Devices screen and clicking the inline red box next to the device as shown below:
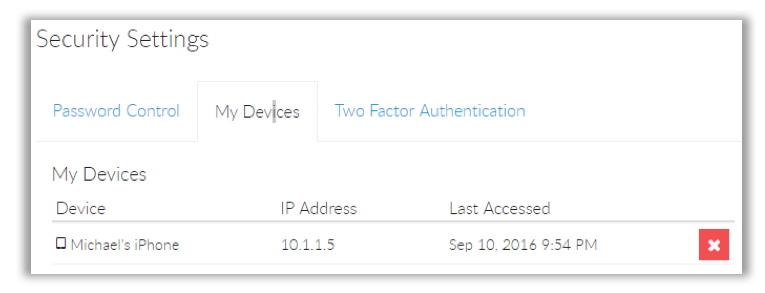
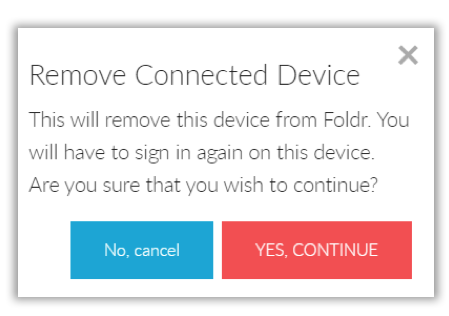
After clicking YES, CONTINUE the device will be revoked and anyone using the device will be unable to log in, even if credentials are stored.
Should they attempt to use the app (and connect to the appliance or interact with it if already logged in) the users account profile in the app is also automatically removed.